How to manage cloud exploitation at the edge
CIO
JULY 17, 2023
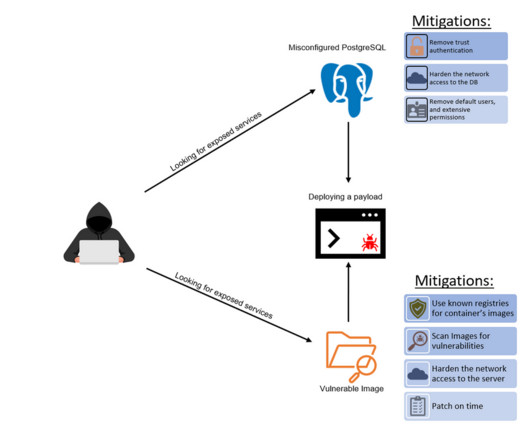
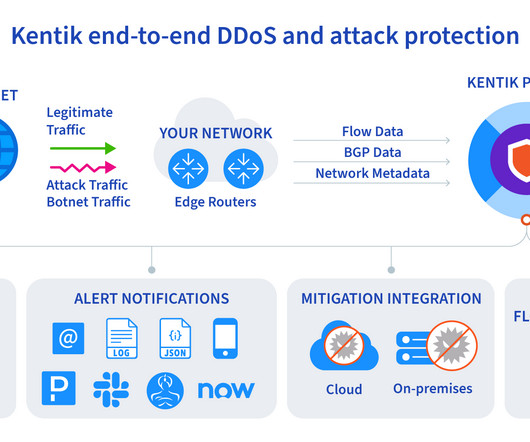
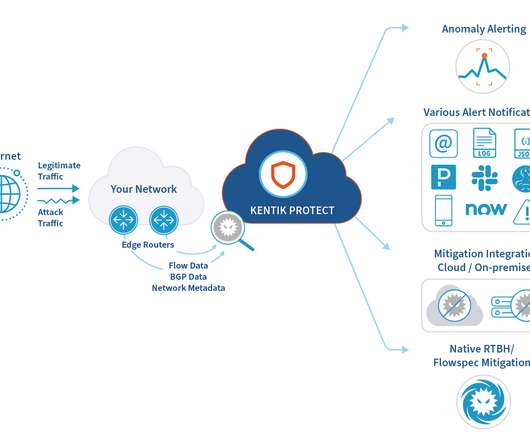
A cloud exploitation playbook could include attack vectors like distributed denial-of-service (DDoS) attacks, web application attacks, and bots – with the number one attack target being web applications. Small- and medium-sized businesses and enterprises have accelerated their move into the cloud since the global pandemic.









































Let's personalize your content