How Can We Strengthen the Cybersecurity of Critical Infrastructure? Here Are My Suggestions for CISOs, Regulators, Vendors – and All Citizens
Tenable
JUNE 1, 2022
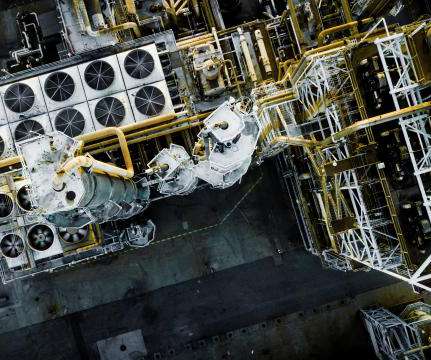
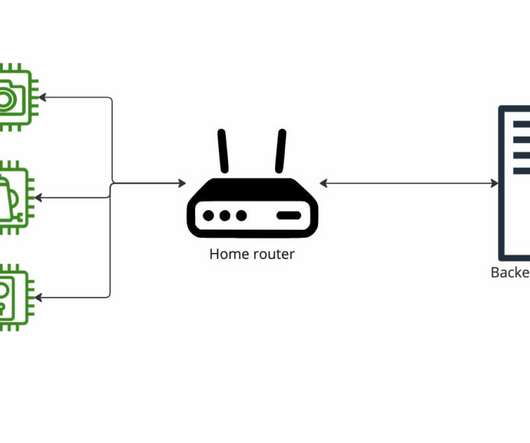
A year after the ransomware attack against the Colonial Pipeline, what can we do to further harden the IT and OT systems of power plants, fuel pipelines, water treatment plants and similar critical infrastructure facilities? government, CISOs, cybersecurity vendors and the public at large. CISOs, CIOs and business leaders.




































Let's personalize your content