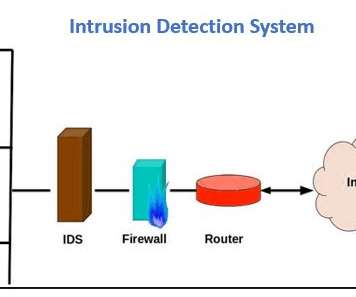
More connected, less secure: Addressing IoT and OT threats to the enterprise
CIO
NOVEMBER 14, 2023
The Internet of Things (IoT) is a permanent fixture for consumers and enterprises as the world becomes more and more interconnected. billion devices reported in 2023. In fact, two notorious botnets, Mirai and Gafgyt, are major contributors to a recent surge in IoT malware attacks.















































Let's personalize your content