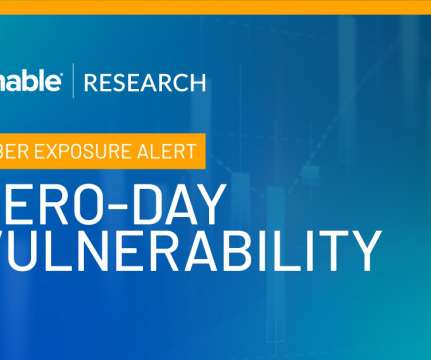
How to minimize remote access cyber security threats in 2024
CIO
JANUARY 22, 2024
Cloud is the dominant attack surface through which these critical exposures are accessed, due to its operational efficiency and pervasiveness across industries. Interestingly enough, high-tech companies were also among the top organizations targeted by threat actors. Address cloud misconfigurations head-on.



















































Let's personalize your content