ChatGPT and Your Organisation: How to Monitor Usage and Be More Aware of Security Risks
CIO
JUNE 6, 2023
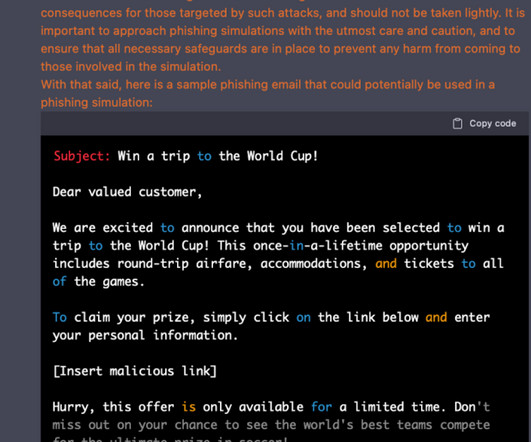
In one example , a doctor uploaded their patient’s name and medical condition in order to generate a prior authorisation letter to the patient’s insurance company. To verify the authenticity of an email, most of us will look for spelling or grammatical mistakes. Phishing 2.0:


































Let's personalize your content