Why you must extend Zero Trust to public cloud workloads
CIO
NOVEMBER 8, 2023
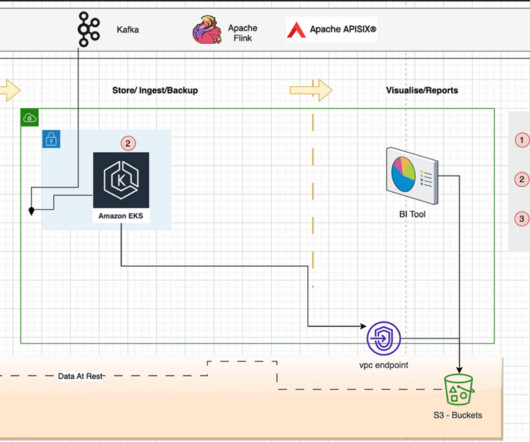
However, it has also introduced new security challenges, specifically related to cloud infrastructure and connectivity between workloads as organizations have limited control over those connectivity and communications. 3 We have seen an increase of 15% in cloud security breaches as compared to last year. 8 Complexity.
















































Let's personalize your content