Optimizing PCI compliance in financial institutions
CIO
JANUARY 4, 2024
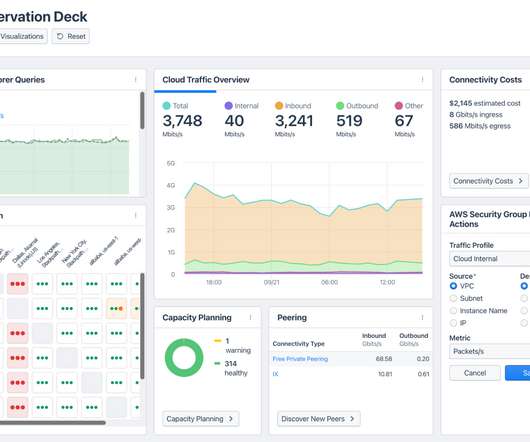
However, managing PCI security compliance across various lines of business within these institutions can be a complex and resource-intensive task. The CCA allows overarching enterprise functions and IT shared services to be assessed separately from the business unit’s products/applications that require PCI security compliance.


















































Let's personalize your content