Providing Customers Greater Flexibility with Managed Detection and Response
Dell EMC
MARCH 6, 2024
Dell Technologies and CrowdStrike expand their partnership by adding CrowdStrike Falcon XDR to Managed Detection and Response.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 detection-response
detection-response 
Dell EMC
MARCH 6, 2024
Dell Technologies and CrowdStrike expand their partnership by adding CrowdStrike Falcon XDR to Managed Detection and Response.

Dzone - DevOps
JANUARY 16, 2024
In highly dynamic cloud-native environments, the traditional Threat Detection and Response (TDR) approaches are increasingly showing their limitations.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
TechCrunch
NOVEMBER 18, 2021
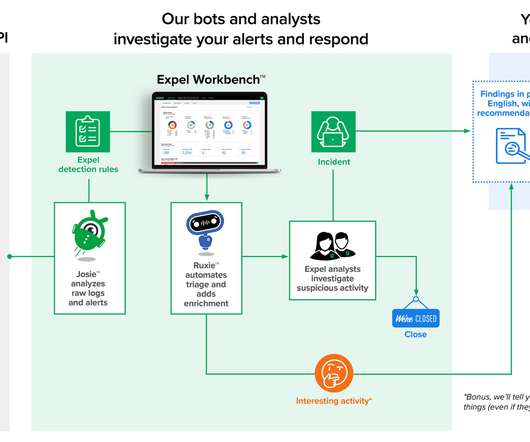
Cybersecurity platform Expel , which specializes in threat detection and response, today announced that it has raised a $140.3

DevOps.com
JANUARY 12, 2021
Managed Detection and Response (MDR), a relative newcomer in the cybersecurity realm, is starting to have a noticeable impact on enterprises seeking to better secure their operations. The post How Managed Detection and Response (MDR) Solutions Benefit DevOps appeared first on DevOps.com. Despite […].
Tenable
JANUARY 19, 2024
With so many tools at their disposal, you might wonder why security teams continue to struggle with detection and response times. Several challenges contributed to the delayed detection. Four cloud incident response challenges Let’s explore why cloud incident detection and response can be so challenging.

Kaseya
OCTOBER 3, 2023
Endpoint detection and response (EDR) is among the latest breed of security software designed to keep emerging and sophisticated cyberthreats like ransomware at bay. The key feature of EDR is its state-of-the-art threat detection and remediation capability that protects you from ransomware-level attacks.

Lacework
MAY 31, 2023
Cloud detection and response (CDR) is a new approach that helps organizations quickly identify, analyze, and respond to potential security threats in cloud environments.

Kaseya
APRIL 6, 2023
Managed detection and response (MDR) service providers give security- and cost-conscious SMBs top-notch threat detection and remediation service that is nearly impossible to build internally. What is managed detection and response (MDR)? Let’s understand how the service works and its benefits.

Lacework
JANUARY 25, 2023
Threat detection and response, commonly abbreviated to TDR, is the process of identifying cyber attacks that are intended to cause harm in an organization’s environment — either on-premises or in the cloud. For years, security teams wrote “rules” to detect new threats based on the identified signatures of previously known threats.

SecureWorks
MARCH 22, 2023
Type: Blogs Why Organizations are Turning to Managed Extended Detection and Response Learn organizations are realizing the full benefits of MDR including faster mean time to detection and mean time to response, cost-effective offloading of detection and response to a dedicated SOC and analyst team

Aqua Security
OCTOBER 13, 2021
Today, Aqua announced the addition of a new, industry-leading detection and response capability to its Cloud Native Application Protection Platform (CNAPP), called Cloud Native Detection and Response (CNDR).

Palo Alto Networks
DECEMBER 10, 2021
Is XDR the future of detection and response? Detection, Response and Analytics. While legacy antivirus morphed into an EPP and next-generation antivirus (NGAV), a separate category of tools emerged to detect and stop endpoint attacks. Two years later, the name evolved to Endpoint Detection and Response (EDR).

TechCrunch
SEPTEMBER 27, 2021
While some of these are very effective, they are only taking on some of the battle, and if an organization wants to adopt the most secure policy, it might use a number of these in tandem, which in turn can slow down systems and response, or create other issues within them. SenseOn does this and more.

Synopsys
APRIL 27, 2023
With the continued move to the cloud, cloud detection and response helps security teams defend their cloud applications and infrastructure.

Kaseya
JULY 2, 2021
And this task starts with choosing a robust endpoint detection and response system. Endpoint detection and response, commonly known as EDR, is a cybersecurity process that gathers and analyzes data collected on the endpoints of an organization — typically the end-user workstations and servers. Who Created EDR?

SecureWorks
DECEMBER 1, 2022
The Right Endpoint Detection and Response Solutions for a Post-Perimeter World The endpoint isn’t the end anymore. Endpoint detection and response solutions – and the environments in which they perform – have changed dramatically. It’s time to rethink how you’re defending it.

SecureWorks
OCTOBER 17, 2022
A Winning Combination: Hardening, Early Threat Detection, and Rapid Response How proactively hardening Active Directory and investing in the Taegis ManagedXDR service quickly contained a breach.

SecureWorks
MAY 11, 2021
Is Endpoint Detection and Response Important for Security Analytics? Endpoint Detection and Response is an important input to security analytics, there’s a reason managed EDR is being replaced with cloud-native SaaS solutions.

IDC
MARCH 18, 2021
The newest security services buzzword is extended detection and response (XDR). Explore the elements of XDR and what you need to know with IDC's Martha Vazquez.

IDC
AUGUST 24, 2023
In the digital business era, transformative advancements have reached unprecedented heights, driving rapid digital transformation and widespread cloud adoption across industries. This transformation has profoundly impacted customer experiences, enabling companies to offer seamless, personalized, real-time interactions across multiple touchpoints.

CIO
MAY 14, 2024
However, two issues have elevated the idea that the technology needs a figurehead to take responsibility for its direction within the agency, something that’s being replicated across other US government departments. It’s important that we remain at the forefront of advancement and responsible use.

Dzone - DevOps
JUNE 7, 2022
What Is DevSecOps? DevSecOps is a collaborative effort by developers, security, and operations teams to get products to market securely and efficiently. This hybrid development and security model aims to address flaws that arise from the relegation of security to the end of the development process.

Palo Alto Networks
APRIL 23, 2020
The evolution of managed detection and response (MDR) within the enterprise has a significant impact on the modern security operations center (SOC). The underlying technology that provides the foundation for data detection and investigation is extremely critical. Quality and Richness of Data for Analytics.

SecureWorks
JUNE 16, 2021
Remove Complexity with Effective Managed Detection and Response Services Ease your cybersecurity management burden with a holistic MDR solution Organizations who rely on multiple security tools for managed detection and response solutions often struggle to get the most value from those tools.

IDC
FEBRUARY 17, 2021
Explore the evolution of managed security services, including managed detection and response (MDR) and SOC-as-a-Service with IDC's Martha Vazquez.

IDC
JUNE 24, 2020
A new subset of security services & providers have emerged to provide managed detection & response (MDR). Define and explore MDR with IDC's Martha Vazquez.

SecureWorks
FEBRUARY 13, 2020
Black Hat 2019: Meet the Future of Threat Detection and Response The future is bright for cybersecurity – and Secureworks® is headed to Black Hat 2019 to show you why. The future is bright for cybersecurity – and Secureworks® is headed to Black Hat 2019 to show you why.

Lacework
OCTOBER 6, 2022
Security monitoring agents are powerful and effective tools for detecting threats in cloud workloads; however, Lacework Labs recently discovered vulnerabilities that would allow attackers to bypass them. To protect your workloads, cloud users must understand how attackers can evade those agent detections. .

CTOvision
MARCH 21, 2018
ProtectWise™ provides cloud-powered Network Detection and Response (NDR). ProtectWise provides a disruptive utility model for enterprise security, delivering pervasive visibility, automated threat detection and unlimited forensic exploration on-demand and entirely from the cloud.

CIO
MARCH 4, 2024
This rapid change demands a rapid response, but the strength of that response depends greatly on two factors – the agility of systems and processes and the availability of skilled workers to run them.
SecureWorks
JULY 15, 2020
Join Secureworks at Black Hat USA To See Software-Driven Threat Detection and Response In Action Visit our virtual booth for a practical demo using a real attack scenario. Our experts are on stand-by to show how machine and human intelligence can be unified to identify malicious threats and stop attacks.

CIO
OCTOBER 25, 2023
This post explains several recommendations for better preventing, detecting, and/or containing a security incident targeting IdPs. A simple deception strategy can help detect adversary presence before an attacker establishes persistence or exfiltrates data. Defense-in-Depth (DiD) plays a very critical role in breaking the attack chain.

CIO
DECEMBER 19, 2023
Real time response systems Inaccurate or incomplete information can slow down and hinder public safety efforts. A real time response system can give a holistic view of safety and security in public transport operations at any given moment. The data the sensors collect on the rails and locomotives is analyzed in near real-time.

CTOvision
MAY 8, 2015
Endgame just launched its first enterprise product, Endgame Enterprise, at RSA last week.Endgame Enterprise is the industry’s first endpoint detection and response (EDR) platform that delivers early warning, instant detection, and active response to advanced threats.
TechCrunch
DECEMBER 19, 2023
Okta, the identity and access management company, is acquiring security firm Spera.

Symantec
JULY 15, 2019
Why is threat detection and response getting harder? Recent ESG research explains why

CIO
APRIL 30, 2024
By processing data at or near the point of creation, edge computing reduces latency, improves real-time responsiveness, and minimizes the need for data transmission to centralized cloud servers. In applications where real-time responsiveness is critical, minimizing latency is paramount. over 2023 2.

SecureWorks
FEBRUARY 13, 2020
Managed Detection and Response Takes Security to the Next Level In the digital era, enterprises of all sizes must be proactive instead of reactive when it comes to cybersecurity. In the digital era, enterprises of all sizes must be proactive instead of reactive when it comes to cybersecurity.
CIO
JULY 17, 2023
Companies that have embraced the cloud need to understand the Shared Responsibility Model: a security and compliance framework that explains what shared infrastructure and systems the cloud provider is responsible for maintaining and how a customer is responsible for operating systems, data, and applications utilizing the cloud.

CIO
MARCH 5, 2024
Google’s FAQ page for Gemini clearly states it will get things wrong and invites users to report responses that need correction. Similarly, ChatGPT’s FAQ page also warns it may provide incorrect responses and invites users to report them. Can LLMS be free from bias? And Giri said, they should focus on using good-quality training data.

Dzone - DevOps
JUNE 7, 2022
What Is DevSecOps? DevSecOps is a collaborative effort by developers, security, and operations teams to get products to market securely and efficiently. This hybrid development and security model aims to address flaws that arise from the relegation of security to the end of the development process.

CIO
OCTOBER 30, 2023
CIOs are responsible for much more than IT infrastructure; they must drive the adoption of innovative technology and partner closely with their data scientists and engineers to make AI a reality–all while keeping costs down and being cyber-resilient. If a threat is detected, then proactive responses kick in to minimize threat proliferation.

CIO
APRIL 25, 2024
We wanted [responses] to be factual but also empathetic. So, among LinkedIn’s first lessons was the importance of tuning LLMs to audience expectations — and helping the LLMs understand how to be perhaps not human, but at least humane with its responses. How do you train the person to write the right response?

CIO
MARCH 26, 2024
By isolating threats that have evaded detection tools and made it to endpoints, HP Wolf Security gives an insight into the latest techniques used by cybercriminals, equipping security teams with the knowledge to combat emerging threats and improve their security postures.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?

Let's personalize your content