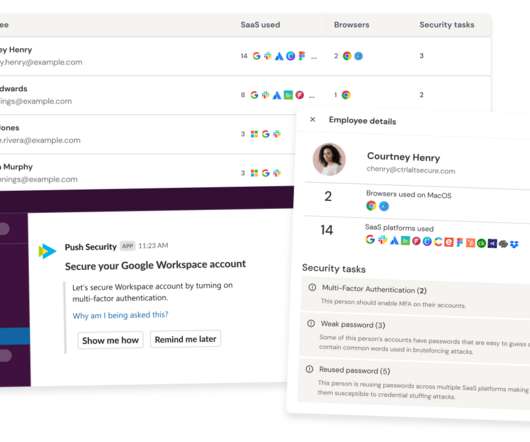
How to implement zero trust device security
CIO
MAY 24, 2024
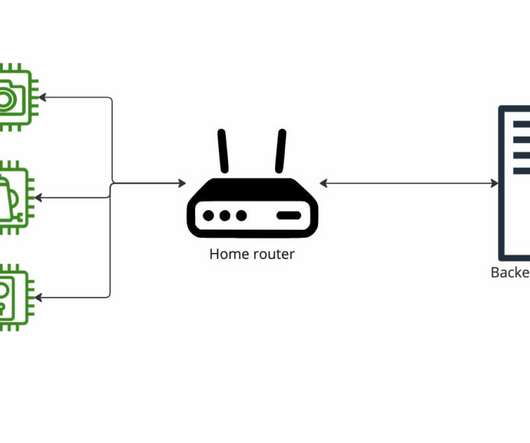
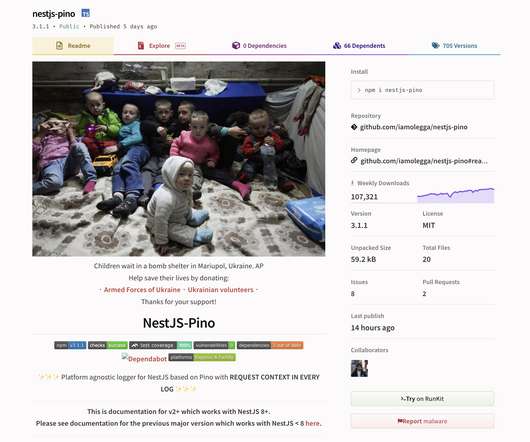
The added demand for remote access to corporate applications driven by business continuity, customer reach, and newfound employee satisfaction comes with a heightened concern over data security. Zero Trust principles are aimed at improving cybersecurity and have been mandated in the federal arena since 2022.














































Let's personalize your content