The rise of AI in software development
Synopsys
AUGUST 11, 2023
Generative artificial intelligence tools are changing the world and the software development landscape significantly. Our webinar series will help you understand how.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Synopsys
AUGUST 11, 2023
Generative artificial intelligence tools are changing the world and the software development landscape significantly. Our webinar series will help you understand how.

DataRobot
APRIL 27, 2021
With these technologies, business users can easily build, deploy, and manage software robots that emulate humans actions interacting with digital systems and software. The benefit of these software robots is they can perform these actions faster and more consistently than people and can run 24/7.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
CIO
JULY 17, 2023
Companies that have embraced the cloud need to understand the Shared Responsibility Model: a security and compliance framework that explains what shared infrastructure and systems the cloud provider is responsible for maintaining and how a customer is responsible for operating systems, data, and applications utilizing the cloud.

Tenable
DECEMBER 16, 2020
The hack, which reportedly involved malicious code embedded in what appeared to be legitimate updates to SolarWinds Orion software, rightfully creates doubts about the security of software supply chains. . In addition, we are closely monitoring our own software development practices.

Tenable
JULY 7, 2023
Learn about the promise and peril of generative AI for software development – and how it makes business execs both happy and fearful. So says a new study from McKinsey, based on a weeks-long test involving 40 McKinsey developers who completed tasks with and without the help of generative AI tools. And much more!

Tenable
DECEMBER 15, 2023
The AI Safety Initiative already has more than 1,500 participants, and these four core working groups have started meeting: AI Technology and Risk Working Group AI Governance & Compliance Working Group AI Controls Working Group AI Organizational Responsibilities Working Group Interested in joining?

Tenable
DECEMBER 22, 2023
The study found only 21% have GenAI usage policies; only 38% are actively mitigating its cybersecurity risks; and 28% are mitigating its compliance risks. Cyber Safety Review Board (CSRB) spotlighted IAM security in its August report of the Lapsus$ cyber extortion group. Among those, 548 are using GenAI.

Ivanti
JUNE 20, 2023
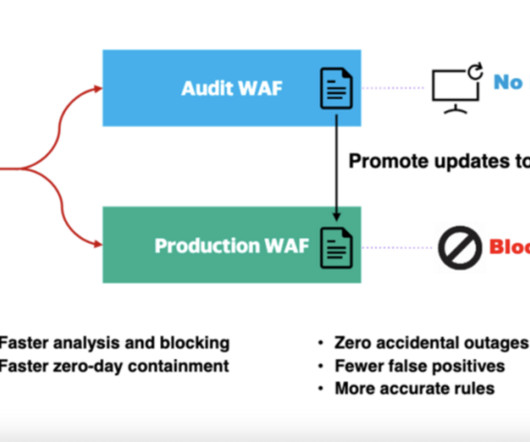
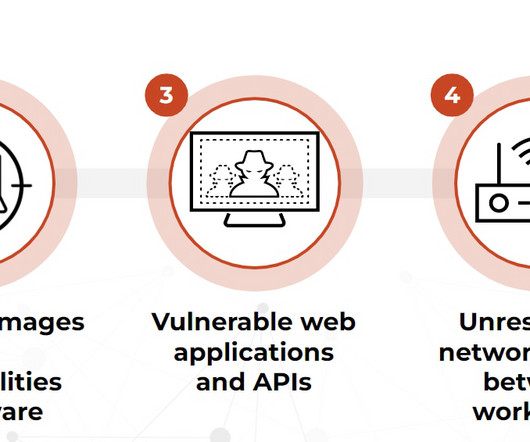
The code that makes up your software applications is another area where complexity contributes to the size of your attack surface. Work with your development team to identify where opportunities exist to minimize the amount of executed code exposed to malicious actors, which will thereby also reduce your attack surface. #2:
Hacker Earth Developers Blog
JANUARY 26, 2023
7 Best HR communities for HR professionals Let’s review the best HR communities you can join to make a difference: 1. For example, you could get tips on how to develop a training program, conduct employee pulse surveys , or even improve company culture. But HRtoHR isn’t just a place to learn and connect.

Ivanti
AUGUST 28, 2023
Review your current supply chain security flaws. The Directive also introduces hefty fines and sanctions for non-compliance, up to a maximum of €10 million or 2% of an organisation's global annual revenue ( Article 34 ). Innovating by adopting new technologies, developing new products or services, creating new markets and more.

Tenable
AUGUST 2, 2023
Confusion over the scope of customer responsibility for cloud security causes control gaps and exposes businesses to risks of attack and non-compliance. Public cloud providers hold multiple industry-specific compliance attestations, (e.g., The top shows the customer’s responsibility for "security in the cloud". Transparency.
Prisma Clud
MARCH 7, 2023
Change also cycles rapidly, particularly with cloud-native application development, where everything from IP addresses to containers is ephemeral. This is the first time cloud native is at the forefront of application development. Feature 2: Rates at which organizations deploy code to production or release to end users.

Tenable
SEPTEMBER 8, 2023
1 - Study: Being a cyber pro is tough, and it ain’t getting any easier Most cybersecurity professionals feel their jobs are getting harder, due to factors like staffing shortages, tighter budgets, growing compliance requirements and increasingly complex attacks. Security Spotlight - Episode 1: The Ransomware Ecosystem Tenable.ot

Palo Alto Networks
OCTOBER 9, 2020
I propose that there are three fundamental and concrete practices DevOps and security teams can adopt to add security into the CI/CD pipeline and secure critical applications, involving: Infrastructure-as-Code (IaC). But they cannot be expected to be experts on the code for every business application. Kubernetes application manifests.

Tenable
DECEMBER 9, 2020
Unpatched hardware, software and configuration vulnerabilities in home devices can now be exploited and leveraged to attack enterprise networks. . At Tenable, we've identified the following global privacy and cybersecurity policy challenges and expected developments that cybersecurity professionals need to monitor in 2021: .

CollabNet VersionOne
MARCH 19, 2018
Managing file versions and meticulously reviewing code for errors can be a dull subject. In fact, it rarely makes the headlines — even in software development news when there are far more exciting trends to cover like AI or the latest Apple device hitting the market. Common Software Development Values.

Honeycomb
JULY 20, 2023
Put simply, incident management is the way an organization reacts to any kind of outage (security, broken code, severe weather, or anything that’s disruptive to customer service). Don’t forget about compliance requirements and state and federal laws. Conclusion Incident management is a fact of modern software development life.

Tenable
MAY 4, 2022
Cloud breaches are on the upswing due to preventable misconfigurations. Over 30 billion records were exposed in 200 breaches between 2018 and 2020 due to cloud infrastructure misconfigurations alone. Here’s how you can lower your risk with a new integration between Tenable.cs and Terraform Cloud. and Terraform Cloud Run Tasks. .

Tenable
FEBRUARY 3, 2023
The new framework is intended to help AI system designers, developers and users address and manage AI risks via “flexible, structured and measurable” processes, according to NIST. “It The launch late last year of the generative AI ChatGPT chatbot has triggered feverish discussions globally about AI benefits and downsides.

Tenable
FEBRUARY 9, 2024
Consequently, it’s critical to develop quantum-resistant encryption algorithms in order to prevent a global data-theft disaster. Expected to be available by 2030, quantum computers will be able to decrypt data protected with today’s public-key cryptographic algorithms.

Altexsoft
AUGUST 9, 2023
Features such as expense management, policy compliance, risk management , and detailed reporting are critical in a corporate travel booking system. Such software aims to streamline the process of sourcing, booking, and managing travel services. B2C vs. B2B booking software: What is the difference? B2B vs B2C travel platforms.

Security Innovation
FEBRUARY 26, 2019
Why You Should Not Rely on Your Developer's as Privacy Experts. Today’s developers have a lot of responsibilities. Adding even more responsibility, recent data privacy legislation also places demands on how development teams store, share, and process their users’ data. Create a data archival, retention, and deletion policy.

Palo Alto Networks
MAY 2, 2019
And it’s even more of a challenge for healthcare organizations when security isn’t centrally managed by anyone, but instead is managed by the CIOs, operations, development and remote office teams. You can learn more in our new eBook, Continuous Monitoring and Compliance in the Cloud. Don’t worry – there’s good news.

Capgemini
MAY 5, 2020
Companies realize the impact of optimized processes to support their digital transformation, yet a constantly growing IT landscape, legacy systems, unharmonized processes, process non-compliance, and a lack of automation all contribute to operational inefficiencies. Cross-sector subject-matter expertise. Register to join us on May 19, 2020.

RapidValue
APRIL 23, 2019
Regulatory compliance can hold organizations back as well as the risks or uncertainties involved in turning to technologies which may appear unproven. Mortgage owners, for example, could benefit from digital analysis which not only gives them a quicker answer, but also develops a more tailored package to their needs.

Hu's Place - HitachiVantara
JANUARY 3, 2019
A data center is like an IoT microcosm, every device and software package have a sensor or log and is ripe for the application of artificial intelligence (AI), machine learning and automation to enable people to focus on the business and not on infrastructure. .”

Altexsoft
JUNE 10, 2022
Still, medical staff can get reimbursed for their efforts due to special programs by the Centers for Medicare and Medicaid ( CMS ) — chronic care management, principal care management, and transitional care management. Below is a table with the Current Procedure Terminology (CPT) codes created specifically for PCM services.

CIO
SEPTEMBER 12, 2022
Data center and cloud services such as infrastructure as a service (IaaS), software as a service (SaaS), platform as a service (PaaS) and anything as a service (XaaS). Data centre mainframe, servers, storage, converged infrastructure, power distribution units, software maintenance and support, co-location and workload migration services.

Tenable
NOVEMBER 17, 2021
Once you have this understanding, you can then proactively apply relevant patches, code fixes and/or compensating controls to mitigate against threats. It is just as important to be aware of configuration and compliance issues. How do I scan for PCI compliance?

Tenable
MAY 3, 2023
Tenable Cloud Security users now can quickly connect their Azure cloud accounts to perform cloud security posture management, including scanning for security vulnerabilities, misconfigurations and compliance. This can lead to a high level of cloud security risks and long remediation times due to manual processes. Here’s how.

Prisma Clud
DECEMBER 13, 2022
I’m excited to share that today at the Palo Alto Networks Ignite '22 Conference we announced impactful capabilities added to Prisma Cloud to help you secure your application lifecycle from code to cloud. For improving code and build security, we have a significant shift-left enhancement, Prisma Cloud Secrets Security.

Altexsoft
JANUARY 27, 2021
In this article, we’ll tell you how front desk software can optimize this process. How front desk software can benefit the hotel business. Using front desk software, you save a lot of time while being much more organized. Everything you do manually can be performed much quicker and autonomously with front desk software.

Tenable
NOVEMBER 11, 2022
That was the topic of a recent Tenable webinar , and we took the opportunity to poll attendees on their Kubernetes usage and on their familiarity with policy as code (PaC), which helps to programmatically ensure compliance with security policies in Kubernetes environments. . Configuring the compilation and build processes.
Mobilunity
DECEMBER 5, 2023
Let’s learn how this role differs from an AI software engineer and which expert your business needs more. These specialists know development methodologies and Machine Learning and usually code in Java, C, and Python. The average AI software engineer salary in the US equals $153,833 per year.

Openxcell
MARCH 11, 2021
It has created a great craze in the mobile app development industry today. Anyone who delivers e-Learning courses uses an LMS Software – and that includes a lot more than educational institutes. Live classrooms and webinar environments for remote instructors and students, client presentations, and much more.

Tenable
OCTOBER 14, 2020
I've run intrusion detection programs and security operations centers and was responsible for policy and compliance of all those components. Develop security policies and procedures that provide adequate business application protection without interfering with core business requirements. I understand the financials.

Ivanti
OCTOBER 26, 2021
Ivanti Azure Device Compliance (formerly from MobileIron). Ivanti Azure Device Compliance allows organizations to update the device compliance status in Microsoft Azure Active Directory (AAD.) Expanded AAD Device Attributes for Compliance Policy Builder. release, please watch the Momentum Webinar recording.

Ivanti
APRIL 20, 2022
First released in 2022 Q1, Ivanti Neurons for Patch Management is a cloud-native patch management solution that helps organizations better protect against threats, including ransomware, by arming them with actionable intelligence on active risk exposure, patch reliability, and device compliance, health and risk. Updated search. Updated APIs.

Tenable
JULY 13, 2021
The vulnerabilities — which affect the company’s EcoStruxure Control Expert, EcoStruxure Process Expert, SCADAPack REmoteConnect x70 and Modicon M580 and M340 control products — pose several risks, including the possibility of complete authentication bypass, arbitrary code execution and loss of confidentiality and integrity. .

Tenable
SEPTEMBER 23, 2022
Outline digital trust goals, identify priorities and develop a road map. Establish a mindset of continuous improvement in areas such as cybersecurity, quality, reliability, compliance and customer experience. 69% said they suffered a security incident due to an unknown, unmanaged or mismanaged attack surface asset.

PowerSchool
OCTOBER 11, 2021
However, the recent pandemic exposed the reality that districts need to move from thinking about software as a support function to a strategic component. Workload Audit applications and software to determine their business value, criticality, and where there are opportunities to modernize. Get the Buyer’s Guide. You might also like.

Saviynt
MARCH 25, 2019
Early in my career, I set some expectations and standards I adhered to: Use the rules: start with compliance defined processes. Self-assess: review whether you met the requirements. Start by securing your people and compliance will follow. Develop a better approach to developers, the cloud, and software-as-a-service.

Cloudera
JUNE 4, 2018
A first cut analysis can enable a review of the content in multiple dimensions: By type: a single unstructured data source may include different types of content (reports, memos, or lab experiments) as well as some low-value information like logs or working files. compliance reporting. compliance reporting.

Tenable
FEBRUARY 23, 2024
Critical Infrastructure ” (Harvard Business Review) 3 - OWASP publishes GenAI governance guide for org leaders Here’s a guide that might interest business and tech chiefs eager to ensure their organizations develop and deploy generative AI securely and responsibly. and Europe, and more than 200 cryptocurrency accounts frozen.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content