Guarding the gates: a look at critical infrastructure security in 2023
CIO
NOVEMBER 7, 2023
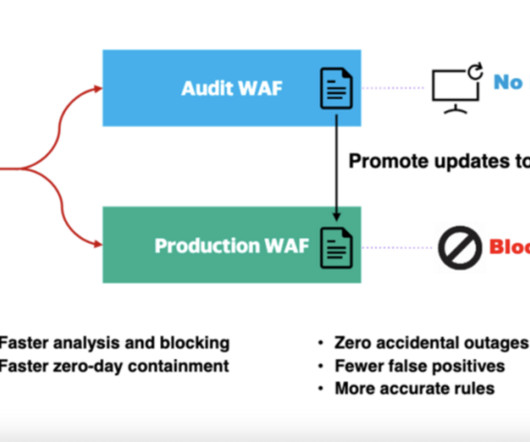
These global events have also underscored the crucial significance of safeguarding our critical infrastructure against domestic or foreign attacks. Navigating the complexities of the modern cybersecurity landscape In this digital age, the field of cybersecurity is becoming increasingly intricate and challenging.


















































Let's personalize your content