CVE-2024-3400: Zero-Day Vulnerability in Palo Alto Networks PAN-OS GlobalProtect Gateway Exploited in the Wild
Tenable
APRIL 12, 2024
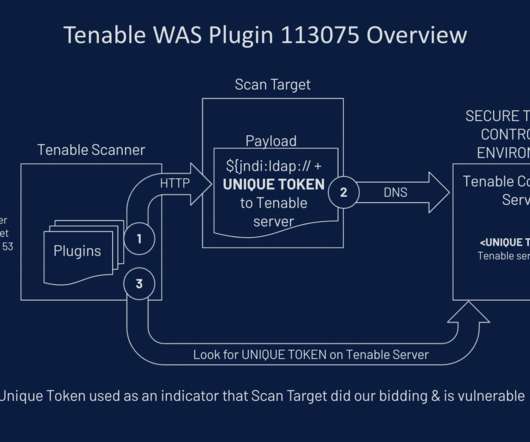
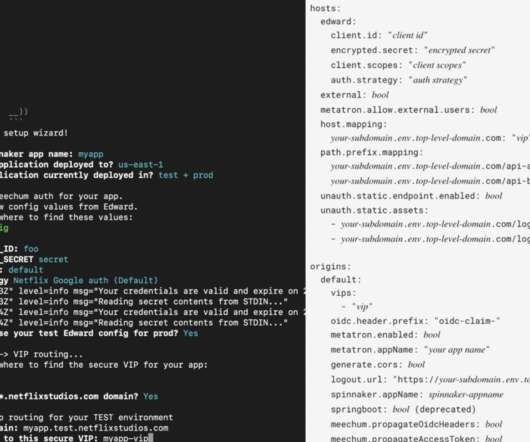
Background On April 12, Palo Alto Networks released a security advisory for a critical command injection vulnerability affecting PAN-OS, the custom operating system (OS) Palo Alto Networks (PAN) uses in their next-generation firewalls. According to the advisory, this vulnerability impacts PAN-OS versions 10.2,
















































Let's personalize your content