Yes, you have to update your Apple devices again, because spyware is bad
TechCrunch
SEPTEMBER 22, 2023
Apple has released urgent security updates for iPhones, iPads, Macs, Apple Watch, and Safari users to block two active spyware campaigns.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

TechCrunch
SEPTEMBER 22, 2023
Apple has released urgent security updates for iPhones, iPads, Macs, Apple Watch, and Safari users to block two active spyware campaigns.
TechCrunch
AUGUST 5, 2023
Poland-based spyware LetMeSpy is no longer operational and said it will shut down after a June data breach wiped out its servers, including its huge trove of data stolen from thousands of victims’ phones. The notice said LetMeSpy is blocking users from logging in or signing up with new accounts.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

TechCrunch
SEPTEMBER 27, 2021
Mobile spyware is one of the most invasive and targeted kinds of unregulated surveillance, since it can be used to track where you go, who you see and what you talk about. And because of its stealthy nature, mobile spyware can be nearly impossible to detect. “We already know applications that are spyware.
TechCrunch
MARCH 29, 2022
Mnuchin, announced today that it is acquiring a majority stake in mobile security startup Zimperium for $525 million. With Zimperium, the firm takes a dive into mobile security, which Mnuchin sees at the front line of cyber security today.

TechCrunch
OCTOBER 4, 2023
Microsoft has released patches to fix zero-day vulnerabilities in two popular open source libraries that affect several Microsoft products, including Skype, Teams and its Edge browser. But Microsoft won’t say if those zero-days were exploited to target its products, or if the company knows either way.

TechCrunch
AUGUST 12, 2023
Also featured are stories about WeWork’s perennial struggles, Google’s Messages app fully embracing RCS, and spyware maker LetMeSpy shutting down after a massive data breach. Taking a page from mobile gaming: Retaining mobile app subscribers is harder than it was last year, but paywall optimization and gamified UX can help.
TechCrunch
MARCH 29, 2023
Alexa, call Grandma” : A new Amazon capability brings T-Mobile customers into the fold for making and receiving calls via an Alexa-enabled device, Ivan reports. Spera raises $10 million for its identity security posture management platform, Frederic reports. Are cryptocurrencies commodities or securities? Is that you, Bob?

O'Reilly Media - Ideas
MARCH 15, 2022
The future of cybersecurity is being shaped by the need for companies to secure their networks, data, devices, and identities. This includes adopting security frameworks like zero trust, which will help companies secure internal information systems and data in the cloud. Zero Trust Security.

TechCrunch
DECEMBER 1, 2023
Apple has released security updates for iPhones, iPads and Macs to patch against two vulnerabilities, which the company says are being actively exploited to hack people. following a vulnerability disclosure by security researchers at Google’s Threat Analysis Group, which investigates […] © 2023 TechCrunch. and macOS 14.1.2,

Altexsoft
JUNE 2, 2020
These insights can help reduce response times and make companies compliant with security best practices. What Is Machine Learning and How Is it Used in Cybersecurity? Machine learning algorithms in cybersecurity can automatically detect and analyze security incidents. The Impact of AI on Cybersecurity.

TechBeacon
SEPTEMBER 16, 2022
Once the message is opened (or, possibly, even if it's not), the victimized endpoint is at the mercy of the spyware’s commands. The story is as old as phishing itself. A malicious message is sent, disguised as something innocuous.

TechCrunch
JANUARY 11, 2022
Today we have new venture funds, spyware news, Brex raising (again), and more. Cybersecurity matters to democracy : Spyware built by the infamous NSO Group was “used to spy on three critics of the Polish government,” according to Citizen Lab, TechCrunch reports. Locket, which is tearing up the mobile application charts.
KitelyTech
SEPTEMBER 27, 2021
Many Android phone users noticed an app called the Mobile Services Manager App on their phones. There is not much information in the system regarding what this app is and what it does. Here is a deeper look at what the Mobile Services Manager App is, what it does, and why it is on your phone. What is Mobile Services Manager?

The Parallax
JANUARY 22, 2018
The digital-rights group Electronic Frontier Foundation and Lookout Mobile Security, which co-authored the report, say they tracked the Dark Caracal phishing campaign across more than 60 websites. “ If you had even a little mobile development experience, [Dark Caracal] could cost less than $1,000.”—Michael

Palo Alto Networks
FEBRUARY 18, 2020
The RSA Conference 2020 is the world’s biggest and most respected gathering of CISOs, technologists and cybersecurity specialists. Last fall, I had the honor of reading through 500 or so submissions from cybersecurity experts eager to take the stage at RSA 2020 (I’m on the committee that chooses presentations).

Tenable
FEBRUARY 22, 2021
When you're new to vulnerability assessment (VA) – or any other area of cybersecurity, for that matter – some aspects of the process might seem unfamiliar or confusing. This is particularly true of the jargon; cybersecurity and technology as a whole have a long list of specialized terminology. . Here’s a brief introduction.

TechCrunch
JUNE 24, 2022
Spyware reaches Android: Security researchers at Outlook recently tied a previously unattributed Android mobile spyware , dubbed Hermit, to Italian software house RCS Lab, Zack reports. It’s intended to help create synthetic data for training AI models in situations where real-world data isn’t plentiful.

Storm Consulting
NOVEMBER 21, 2023
A VPN (Virtual Private Network) can also add a level of reliability to your mobile phone or perhaps tablet, keeping your data and privacy secure when connecting to public Wi-Fi networks. Another major option is normally PIA, that has an extensive characteristic set and a strong mobile application.

Palo Alto Networks
JANUARY 23, 2023
It should come as no surprise that cybersecurity is, once again, priority #1 for state CIOs. Perhaps it’s because none of the other initiatives on the list (not even hybrid work, legacy modernization or cloud adoption) can succeed without a solid cybersecurity foundation. And, they’re innovating faster than ever before.

KitelyTech
JANUARY 11, 2019
Here are five cybersecurity threats to SMEs and how custom software development services Chicago wide can help. In addition, SMEs should have secure backups for crucial data. Examples of malware include spyware, Trojans, adware, ransomware and bots. Poor knowledge of cybersecurity. Internal attacks.

Storm Consulting
NOVEMBER 7, 2023
She has covered all things tech by desktops to mobile devices, and specializes in Apple products. When it comes to virus safety reviews, the most important factor is how well a program helps to protect against spyware and adware. Her favorite component to her task is checking the web for top in tech and then talking about it.

Samanage
JUNE 11, 2019
Information Security, Assets, and IT Security Threats. Then, we’ll talk about how quality IT asset management that includes risk detection and license compliance can enhance your IT security, reduce your organization’s vulnerabilities, and provide real value to your business. Assets are broadly defined as “items of value.”

Lacework
JANUARY 25, 2023
Whether you’re facing a sophisticated phishing attack or a form of never-before-seen malware (also known as an “unknown threat” or “unknown unknown”), threat detection and response solutions can help you find, address, and remediate the security issues in your environment. cryptojacking) and data exfiltration.

Ivanti
SEPTEMBER 9, 2021
Within the initial blog in this series , we discussed ransomware attacks and their remediation on Android mobile devices. Part 2 addresses potential ransomware exploits and their remediation on iOS, iPadOS mobile devices and macOS desktops. Fortunately, security updates exist for these known and former zero-day vulnerabilities.

TechCrunch
FEBRUARY 15, 2022
But first, in an essay on TechCrunch, former Homeland Security Secretary Michael Chertoff argues against “the unfettered ‘side-loading’ of apps.” It is an interesting argument against Windows and the larger Web (we kid), but does raise notable points regarding mobile security and consumer expectations. The latest?

Ivanti
JANUARY 19, 2022
Phishing continues to be the most common type of cybercrime today, and as remote and hybrid work becomes the norm, companies and employees have become more relaxed with their cybersecurity hygiene. It is human nature. Ransomware is malware whose sole purpose is to extort money from the end user. Learn more.

CTOvision
APRIL 28, 2014
For a decade now the cyber security community has been treated to important strategic context coordinated by Verizon in their Data Breach Investigations Report (DBIR). Also, defensive measures keyed to the Critical Controls coordinated by and for the community by the Council on Cyber Security are also provided in each of the attack patterns.

CTOvision
JULY 6, 2015
Mobile apps drive fleet management GCN (Today) - Fleet management apps at the General Services Administration and State Department give agencies real-time data integration between the field and home office.As The law broadly defines national security as covering everything from finance. The [Advanced Anti-Radiation Guided. The health.
O'Reilly Media - Ideas
AUGUST 2, 2021
Security continues to be in the news: most notably the Kaseya ransomware attack, which was the first case of a supply chain ransomware attack that we’re aware of. However, the biggest problem in security remains simple: take care of the basics. Web and Mobile. That’s new and very dangerous territory.

TechCrunch
JULY 15, 2022
Journalists and activists are increasingly targeted by the wealthy and resourceful who seek to keep the truth hidden, from nation-state aligned hackers hacking into journalist’s inboxes to governments deploying mobile spyware to snoop on their most vocal critics. Runa Sandvik, founder of Granitt. Image: (supplied).

Palo Alto Networks
OCTOBER 2, 2019
While the average worker has grown as comfortable using mobile devices as desktop computers, security teams have yet to catch up. Mobile devices have emerged in recent years as the leading platform for cybercrime and cybersecurity threats against organizations. By Evin Safdia, Technical Marketing Manager, Prisma.

Hu's Place - HitachiVantara
MAY 10, 2019
In the past 10 years the incidents of fraud have escalated thanks to new technologies, like mobile, that have been adopted by banks to better serve their customers. Criminal gangs use malware and phishing emails as a means to compromise customers’ security and personal details to commit fraud.

Mobilunity
DECEMBER 30, 2022
If you have an IT team, keep in mind that they don’t always have time to conduct a comprehensive cybersecurity assessment because they are already overwhelmed with day-to-day tasks. Therefore, many businesses hire cybersecurity experts to join their teams and take care of security tasks. Making use of out-of-date software.
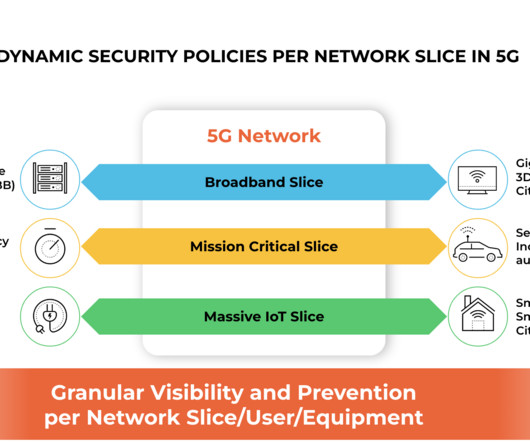
Palo Alto Networks
FEBRUARY 27, 2023
Our work with Singtel focuses on application-layer security, 5G network slice security, intelligent security per 5G subscriber and equipment identities. The role of cybersecurity has become increasingly important. Application-Layer Security Application-layer security has a few dimensions.

Xebia
AUGUST 13, 2021
From the earlier listed website types, it secures the final website product. It is widely used by many casinos and online betting websites over the world, making secured and high quality worldwide websites are characterized by day-to-day data posting and are prone to cyberattacks because of that. Securing Against Malware.

Ivanti
AUGUST 9, 2021
Humans are the weakest link in the cybersecurity chain. Enter FIDO2 security keys to kill off the password! In the case of Ivanti’s Zero Sign-On , your company can implement a FIDO2 solution by using your managed iOS or Android mobile device as a replacement for the security key. Where have you heard that before?
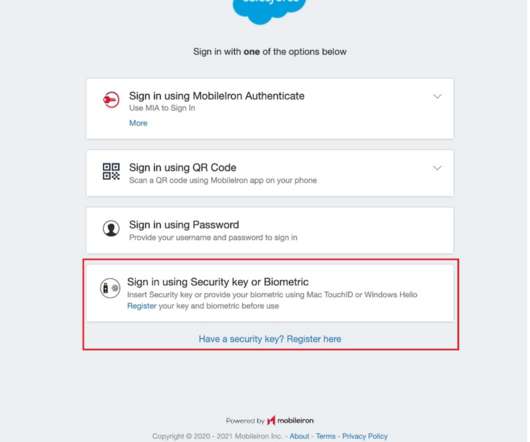
Ivanti
DECEMBER 29, 2021
Eliminating passwords just makes too much sense as it raises your company’s Zero Trust security maturity level by removing the most common root cause of data breaches. FIDO2 leverages the stronger authentication factors, with biometrics as the inherence factor and your mobile device as the possession factor.

Kaseya
NOVEMBER 3, 2020
But before we announce the winners, let’s take a brief look at the sinister cybersecurity threats that plagued our Haunted House of IT and the weapons the survivors procured to protect themselves against these threats. Keeping your software up to date by applying the latest security patches is an aboslute must. The Threat: Malware.

Kaseya
OCTOBER 28, 2021
Over the last few years, we have grown accustomed to hearing about cybersecurity incidents affecting companies of all scales and sizes. Despite a robust cybersecurity perimeter in response to growing threats, cybercriminals always seem to find a way around it. In 2021, a data breach cost an average of $4.24 million, up 10% from $3.86

Kaseya
DECEMBER 28, 2021
Endpoint protection, also known as endpoint security, involves the use of advanced security tools and processes to secure various endpoints like servers, workstations and mobile devices that connect to a corporate network. The global endpoint security market is projected to continue to grow to over $19 billion in 2025.

Tenable
OCTOBER 7, 2022
7 | CISA puts spotlight on asset inventory and vulnerability management | Think tank does deep dive on IoT security | What’s the current state of cybersecurity? As Cybersecurity Awareness Month kicks off, here’s a fresh reminder from the U.S. Cloud Security: Why You Shouldn’t Ignore Ephemeral Assets.

TechCrunch
AUGUST 23, 2022
Hear from its creator Anatoly Yakovenko about the opportunities and challenges ahead as Solana seeks to take web3 to mobile devices in a push for mass adoption. How To Secure Those Hard-To-Find Hires. with Brett Callow (Emsisoft) and Katie Moussouris (Luta Security). TechCrunch Startup Battlefield — Session 4. with Peter A.
O'Reilly Media - Ideas
AUGUST 2, 2022
Perhaps the scariest exploit in security would be a rootkit that cannot be detected or removed , even by wiping the disk and reinstalling the operating system. AWS is offering some customers a free multi factor authentication (MFA) security key. Minerva has also been trained and tested in chemistry and physics.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content