10 things to watch out for with open source gen AI
CIO
MAY 15, 2024
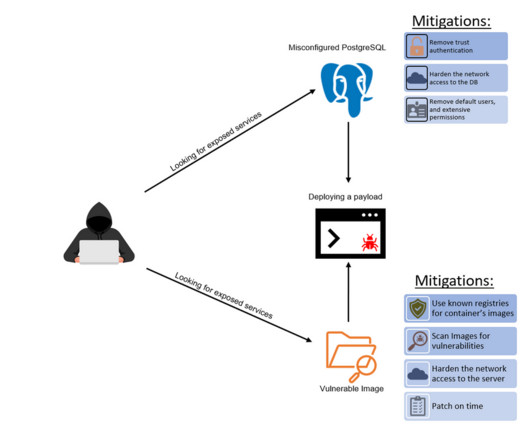
It takes expertise to download the open source version,” he says. In addition, vendors have access to the prompts that users send to the public versions of the models, so they can monitor for signs of suspicious activity. Another attack vector is the model’s system prompt. It’s not just trial and error,” says Rao.










































Let's personalize your content