PCI DSS version 4.0: Is your payment card data security program ready?
CIO
OCTOBER 16, 2023
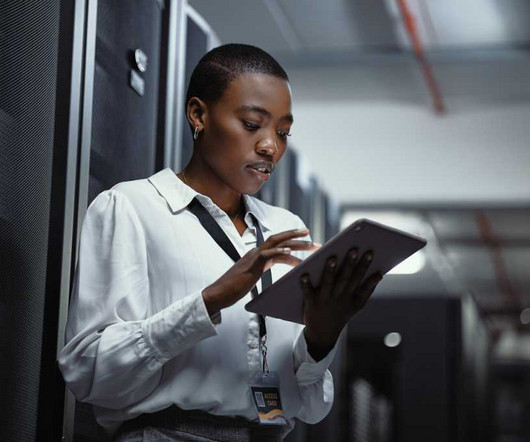
The numerous new attack vectors being used by threat actors to obtain payment card data underscores the increasing necessity of compliance with the Payment Card Industry Data Security Standard (PCI DSS). and remain compliant long-term, while continually strengthening their overall security stance.















































Let's personalize your content