SD-WAN Helping Financial Services Achieve Greater Digital Agility, Cybersecurity
CIO
JULY 11, 2022
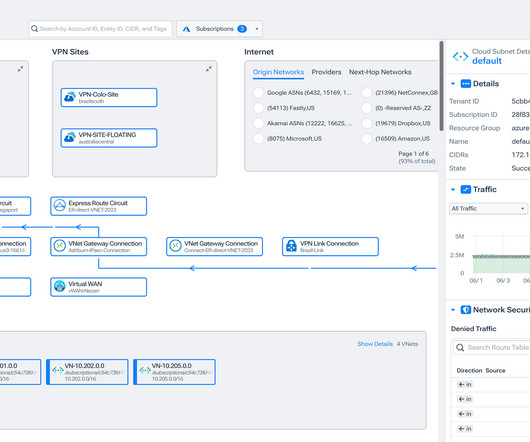
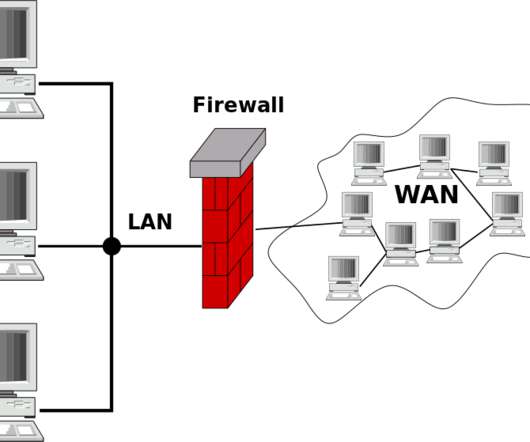
However, for many financial services organizations, security and agility traditionally haven’t been mutually achievable—oftentimes, one was sacrificed for the other. SD-WAN can help financial services organizations achieve network agility and security. During the pandemic, that threat multiplied exponentially.














































Let's personalize your content